De Magie van Cazeus Casino Beleven
November 3, 2025Analyse complète du casino en ligne Cashed pour les joueurs français
November 3, 2025Wow!
I was poking around different Solana wallet extensions last night, honestly just curious. My instinct said some of these felt rushed. Initially I thought newer wallets were mostly about prettier UI. Actually, wait—let me rephrase that: the UI matters, but the real differences show up when you sign dozens of transactions and one of them fails. On one hand the flashy onboarding wins users fast; on the other hand, reliability and recovery are what keep me using a wallet for months.
Really?
Transaction speed on Solana is fast, obviously, but the extension’s architecture can bottleneck that speed. I noticed one wallet that queued transactions oddly when the browser tab lost focus. Something felt off about its background worker handling. My instinct said the devs prioritized visuals over robustness. That bugs me, because when money’s involved you want rock-solid behavior.
Whoa!
Security is the part most people talk about—and they should. But there are layers to security beyond seed phrases and hardware keys. For example, extension permission scopes, how often the extension prompts for confirmation, and whether it isolates dApp sessions matter a lot. Initially I thought “permissions = permissions” but then realized a permission model can be proactive or permissive, and that affects long-term safety. I’m biased, but I prefer the proactive kind.
Hmm…
I tried a few approaches to test wallets: repeated transfers, dApp interactions, and simulated recoveries. I purposefully broke a local device and tried recovering the account from seed. Recovery went smoothly in some extensions and clunkily in others. My working theory changed as I tested more; recovery UX isn’t glamorous, yet it’s one of the most important features. So yeah, somethin’ as boring as recovery can make or break trust.
Here’s the thing.
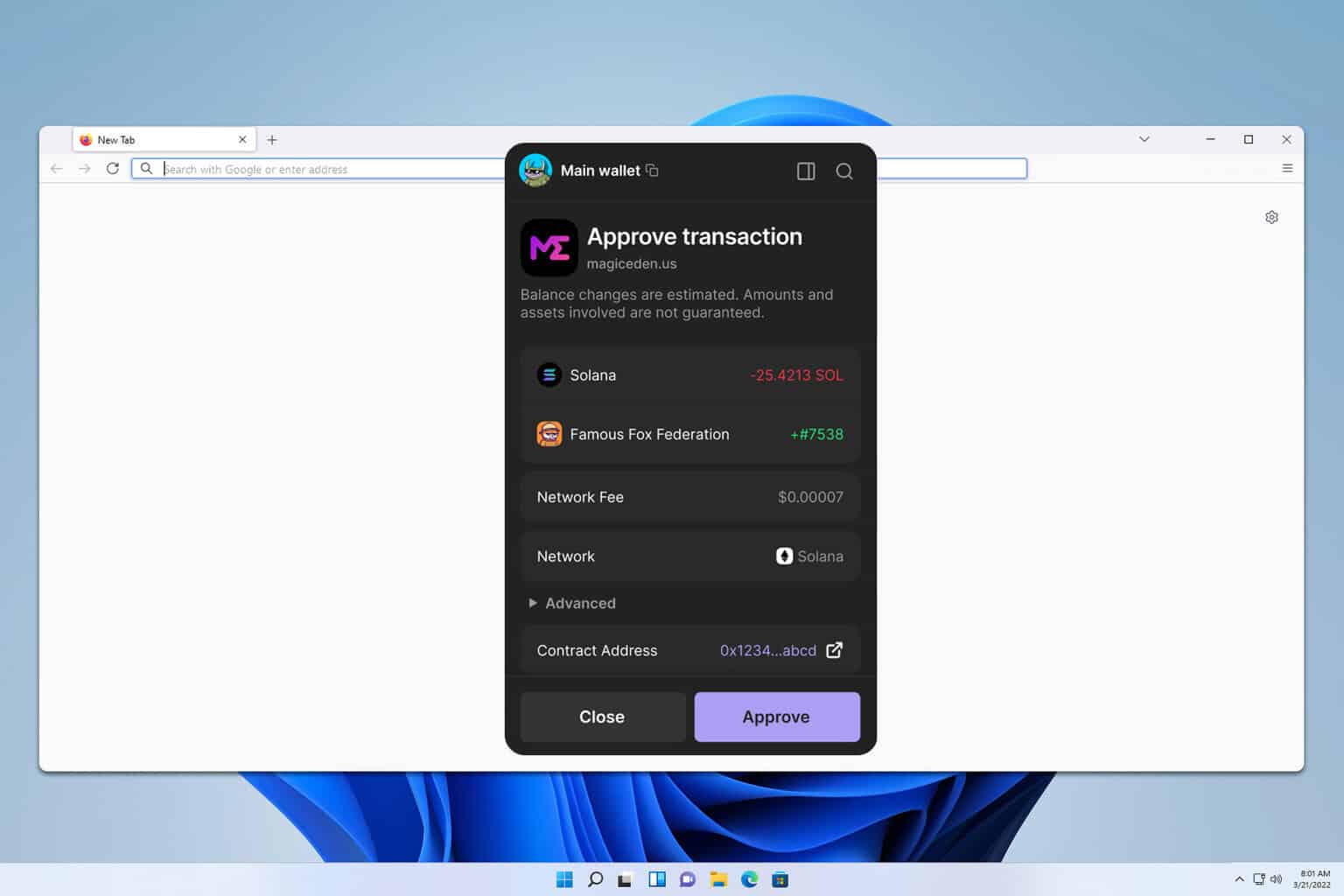
What’s nice about modern Solana extensions is that they increasingly support hardware wallets, multisig, and transaction previews. But not all implementations are equal. Some show full instruction details and RPC calls; others hide the guts and leave you guessing. On a technical level this matters for power users and for those who want to verify actions before approving them, which I do every time—very very important to me.
Okay, quick aside—
Performance also depends on how the extension caches recent activity and how it talks to RPC endpoints. If it uses public RPCs only, you’ll see spikes and throttling during network congestion. If it supports configurable RPC endpoints or built-in fallbacks, your experience is smoother. (Oh, and by the way: latency matters when you’re minting a drop; milliseconds can matter.)
What I actually use and why
I’ll be honest: I keep coming back to one extension for day-to-day use because it nails the balance of UX and security. The extension I’m talking about offers clear transaction previews, sensible permission prompts, hardware wallet compatibility, and a recovery flow that just works even when you panic. I linked to it here because it helped me through a messy restore once—check out the phantom wallet download page if you want to see their extension flow yourself. I’m not trying to shill; I’m sharing what worked in my messy, real-world tests.
Seriously?
Yes—because the small things add up. For example, one extension shows the program IDs and instruction bytes in an expandable panel, which helps me audit approvals quicker. Another groups dApps by domain and warns when a domain requests unusual permissions. Those are the features that stop me from blindly approving things. On balance, the safer defaults win my trust.
Alright, but there are tradeoffs.
Extensions that do too much UI work can slow down browsers, and some people prefer a minimalist approach that delegates heavy lifting to hardware or mobile. On the flip side, minimalist extensions sometimes forget to explain cryptic Solana errors to users. So on one hand you get speed and simplicity; though actually—if the app can’t tell you why a txn failed, you’re stuck troubleshooting with dev tools. That part bugs me.
Honestly, this is where I see the ecosystem maturing.
Developers are iterating quickly and users are getting choosier. Wallet extensions now offer per-dApp permissions, curated sets of RPCs, integrated swap widgets, and sometimes staking helpers. But the market still needs better standards around transaction transparency and recovery UX. I’m not 100% sure what the final standard will look like, but the direction is encouraging.
Here’s another thought.
For new users, mobile-first wallets often feel easier, but extensions bridge the gap to browser dApps. If you want both speed and control, an extension that supports hardware keys and clear permissioning is ideal. Initially I thought mobile wallets would eclipse browser extensions, but after testing, browser extensions remain crucial for many desktop-centric dApps. So the ecosystem needs both, working together.
Common questions
How do I pick a Solana extension wallet?
Look for clear transaction previews, hardware wallet support, and sensible permission prompts. Check recovery flow by doing a dry run (create a secondary account and test restore). Also, see if the extension lets you choose or add RPC endpoints—this reduces reliance on congested public nodes. I’m biased toward wallets that are transparent about program IDs and instruction details, because that transparency reduces surprises.
Is using a browser extension safe?
Yes, with caveats. Extensions are safe when they use good permission isolation, don’t leak secrets, and support hardware wallets for high-value transactions. Watch out for extensions that require excessive permissions or ask to export private keys plainly. If somethin’ smells off—stop. Seriously, stop and verify before approving anything.